Basics of UEFI and Secure Boot
SummaryThis blog aims to give a concise introduction to the basics of UEFI and Windows support for UEFI.
Baics of UEFI
In general terms, UEFI (Unified Extensible Firmware Interface)is a replacement for BIOS which defines a software interface between an OS and platform firmware. UEFI simplifies the process of interoperating firmware and OS – makes it easy to run one OS on different hardware platform, for example, an OS can run on devices from different manufacturers . The following diagram illustrates a simplistic case of how OS-UEFI-Firmware-Hardware interact:

In the above case, because of the standard UEFI API GetTime(…), when the clock manufacturer changes, there is no need to change the OS. Only the firmware’s GetTime(…) implementation needs to change. This is normally done by the clock manufacturer to implement theGetTime() interface.
UEFI Components
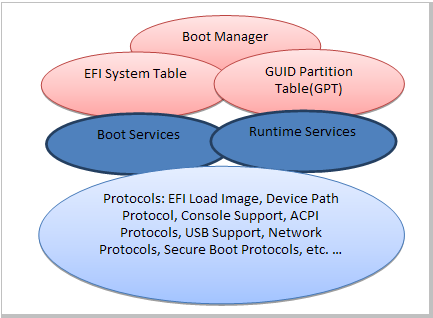
Boot Manager controls from which media to boot the system, which environment to boot to, for example, emergency download, UEFI shell or normal OS.
Boot Services define interfaces to boot an OS image. Some sample services are
- LoadImage(…)
- StartImage(…)
- UnloadImage(…)
- Exit(…) – Exists from a started image.
- ExitBootServices(…) – After an image is started, main OS calls this function to terminate the Boot Service and take over control of the system.
Runtime Services are available pre- and after main OS boot. These are the core services that makes an OS be able to run. These services include
- Variable services – Allows OS to store/retrieve key/value pairs before it can actually access any file system. These key/values pairs are most often persistent, thus requiring nonvolatile storage. For example, remembering hardware failure record during the last boot.
- Time services – Provide services to access the hardware clock
- Virtual Memory services – Allows OS to use virtual addressing mode, rather than flat physical mode.
- GetTime(…)
- SetTime(…)
- GetVariable(…)
- ResetSystem(…)
Protocols The majority of UEFI is made of protocols. The following is a list of protocols:
- EFI Loaded Image
- Device Path Protocol
- UEFI Driver Model
- Console Support
- Media Access
- PCI Bus Support
- SCSI Driver Models and Bus Support
- iSCSI Boot
- USB Support
- Debugger Support
- Compression Algorithm Specification
- ACPI Protocols
- EFI Byte Code Virtual Machine
- Network Protocols, TCP, IP, UDP, FTP etc.
- Security - Secure Boot, Driver Signing and Hash
- HII (Human Interface Infrastructure) Protocols
- User Identification
- Firmware management Protocol
- UsbControlTransfer()
- UsbBulkTransfer()
- UsbAsyncInterruptTransfer()
- UsbSyncInterruptTransfer()
- UsbIsochronousTransfer()
- UsbAsyncIsochronousTransfer()
- UsbPortReset()
- Etc.
All 64 bit Windows OS support UEFI. 32bit OSes do not support UEFI.
The upcoming Windows 8 OS will enable UEFI's secure boot capability using eFueses. In very simple terms, Secure Boot will only allow authorized OSes(Windows 8) to run on the hardware. This means, if you buy a PC configured with Windows 8, you may not install other OSes, including previous Windows OSes. This has raised many concerns and much debate on secrre boot. Below is the statement from Microsoft:
- UEFI allows firmware to implement a security policy
- Secured boot is a UEFI protocol not a Windows 8 feature
- UEFI secured boot is part of Windows 8 secured boot architecture
- If desired, Windows 8 utilizes secured boot to ensure that the pre-OS environment is secure
- Secured boot doesn’t “lock out” operating system loaders, but is is a policy that allows firmware to validate authenticity of components
- OEMs have the ability to customize their firmware to meet the needs of their customers by customizing the level of certificate and policy management on their platform
- Microsoft does not mandate or control the settings on PC firmware that control or enable secured boot from any operating system other than Windows
So, in the very near future, if you buy a PC, it may only run Windows(8).
ReferencesUEFI Specifications
Window Support for UEFI
Microsoft is Going to Block out Other OSes
*** END ***
